Most property management companies assume moving to the cloud made their data more secure. And honestly, in some ways it did. Cloud platforms like Yardi, AppFolio, RealPage, MRI, Entrata, and Buildium come with infrastructure-level security that most PM companies could never build on their own.
But moving to the cloud also introduced risks that did not exist before. New entry points. New attack surfaces. New responsibilities that fall entirely on you, not your vendor.
This guide explains what actually changes about security when your PMS moves to the cloud, where your vendor’s responsibility ends, and what your team needs to do about the rest.
What Changes About Security When You Move to the Cloud
On-premise systems kept everything behind one wall. Your data sat on servers you controlled, in a building you managed, accessible only to people physically or remotely connected to your network.
Cloud changes that completely.
When your operations run through a cloud PMS, your data flows across remote servers, tenant portals, payment processors, maintenance apps, screening tools, and mobile devices used by staff across every property in your portfolio. Every one of those connections is a potential entry point.
The cloud did not make you less secure. It changed where the risk lives.
And the risk is real. Seventy-seven percent of multifamily operators experienced some form of fraud in the past twelve months. Real estate ranked second for ransomware breaches in 2024 with 553 incidents, behind only manufacturing. Ransomware was present in 44 percent of all data breaches in 2025, up twelve percent year over year.
The industry is a target. The question is whether your security posture matches that reality.
What Your PMS Vendor Secures and What You Are Responsible For
This is the part most PM operators do not know until something goes wrong.
Your PMS vendor secures the infrastructure. That means the data centers, the servers, the platform uptime, and the encryption of data moving through their systems. Yardi, AppFolio, RealPage, MRI, Entrata, and Buildium all invest significantly in this layer. Yardi is CSA STAR registered, meaning they publicly document their cloud security controls through the Cloud Security Alliance.
What that certification covers: their infrastructure.
What it does not cover: your user credentials, your access permissions, your third-party integrations, your employees’ endpoints, and your offboarding process when a leasing agent leaves.
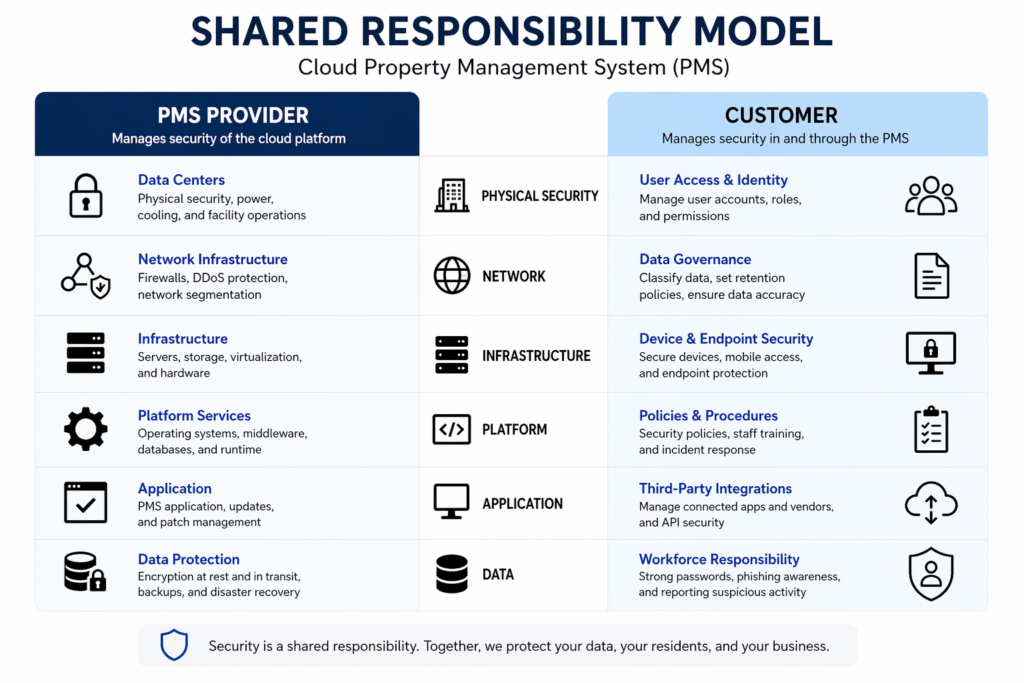
That is the shared responsibility model. Your vendor secures the platform. You secure everything built on top of it.
Most PM companies have never heard the term. Most are operating under the assumption that because their data lives in the cloud, it is protected. It is protected at the infrastructure level. Everything else is yours to manage.
How Property Management Companies Are Actually Getting Compromised
The attacks targeting PM companies are not sophisticated. They do not need to be.
In 2025, attackers ran an active campaign buying sponsored Google ad placements impersonating at least thirteen cloud property management vendors. When a leasing manager searched for AppFolio or Yardi by name, the top result was a fake login page designed to harvest their credentials. The real vendor site appeared below it.
That is how it starts. A leasing agent logs in from a property office. The credentials go to an attacker. The attacker is inside your AppFolio environment before anyone knows something is wrong. From there they have access to tenant records, payment data, and lease files across your entire portfolio.
ACH redirect fraud works the same way, just through a different door. Accounting staff who process vendor payments daily through your cloud PMS are the target. A fake vendor invoice, a spoofed email from a property owner, a redirected ACH payment. The funds are gone before the bank confirms anything.
Former employee access compounds both risks. Site managers and leasing agents turn over constantly. Their Yardi or RealPage logins often stay active for weeks or months after they leave. An attacker with access to a former employee’s email can reset those credentials and walk right in without triggering a single alert.
Third-party integrations add another layer. Every tool connected to your PMS creates another potential entry point. Sixty-five percent of large companies say third-party and supply chain risk is their biggest security barrier in 2026. Most PM operators have never audited the security posture of the tools connected to their Buildium or Entrata environment.
The consequences are not hypothetical. Income Property Management, managing fourteen thousand residential units, had tenant SSNs and passport numbers stolen in a 2025 breach. Real Estate Specialists, a multifamily and commercial PM company, was hit by Qilin ransomware in October 2025. SitusAMC had accounting records and legal agreements compromised in November 2025. Qilin specifically targets real estate and construction. PM companies are on their industry hit list.
Sixty-one percent of property managers lack confidence in their ability to prevent fraud with their current process. That number should be higher.
Security Measures Every Cloud PM Operation Needs
Start with Multi-Factor Authentication. MFA requires a second verification step beyond a password, a code sent to a phone, a biometric prompt, an authenticator app. Every user on every platform, no exceptions. If someone can log into your PMS with only a password, that account is a liability waiting to be exploited.
Next, lock down who can see what. Role-Based Access Control limits each user’s access to what their job actually requires. Your leasing agent does not need financial records. Your maintenance technician does not need tenant SSNs. Your regional manager does not need admin-level permissions across every property. Most cloud PMS platforms have RBAC built in. You have probably never configured it.
Extend that thinking to devices. Every laptop, phone, and tablet that touches your PMS is part of your attack surface. Your on-site manager’s personal phone that she uses to approve maintenance requests in AppFolio needs endpoint protection, antivirus, device management, and remote wipe capability if it is ever lost or stolen.
Before you connect any new tool to your PMS environment, ask whether they hold SOC2 Type 2 certification. SOC2 Type 2 is an independent audit that verifies a vendor’s security controls actually work over time, not just on paper. If a vendor cannot produce it, that is a signal worth taking seriously.
Do not ignore what is already in your platform. Most cloud PMS environments have audit logging built in. You are probably not looking at it. Set up access monitoring that flags unusual login times, unfamiliar locations, and access patterns outside normal activity. A leasing agent logging in from a different state at 2am is worth ten minutes of your time to investigate.
Finally, run a quarterly access review. Pull the full user list from every PMS platform and confirm every account belongs to a current employee with the right level of access. Deactivate anything that should not be there. This single practice closes more exposure than most security tools you could buy.
Why Human Error Is the Biggest Risk in Property Management
Sixty-eight percent of breaches involve a human element. That stat comes from Verizon’s 2025 Data Breach Investigations Report covering over twelve thousand confirmed breaches.
Here is the one that should stop you cold. Verizon’s phishing simulations found that users clicked a phishing link within twenty-one seconds of receiving the email. They entered their credentials within twenty-eight seconds of clicking.
Your leasing agent gets a fake AppFolio password reset notification. Twenty-one seconds later they click it. Twenty-eight seconds after that your credentials are in an attacker’s hands.
Your leasing agents, on-site managers, and accounting staff are the most common entry points. Not because they are careless. Because nobody trained them on what a PM-specific attack looks like. A generic cybersecurity training about not clicking suspicious emails does not prepare someone to recognize a fake Yardi notification or a spoofed vendor invoice inside their normal workflow.
Ninety-seven percent of AI-related breaches lacked proper access controls. Attackers are using AI to craft phishing messages that are indistinguishable from legitimate vendor communications. The fake AppFolio email looks exactly like the real one. The fake Buildium alert reads perfectly. Standard phishing training is not keeping up.
A security awareness program for your distributed team needs to be short, scenario-based, and repeated quarterly. Show your leasing agents what a fake Yardi login page looks like. Show your accounting team what a spoofed vendor invoice looks like. Run a simulated phishing test. Track who clicks. Retrain the ones who do.
How MSPs Support Better Data Security
Building and maintaining this security posture requires someone who owns setup, monitoring, access reviews, training, and incident response. All of it. On an ongoing basis.
For most PM companies that person does not exist. Or they exist and they have forty other priorities that are more urgent than running a quarterly access review or checking audit logs for unusual login activity.
An MSP takes all of it off the table. Your MFA is deployed and enforced across every platform. Your access reviews run on a defined schedule without anyone on your team thinking about it. Your endpoint monitoring covers every location in your portfolio. Every new third-party integration gets vetted before it goes live.
See also: The Top 10 IT Companies For Property Managers
Before you sign with any MSP, ask three things. Do they understand how user permissions actually work inside Yardi, AppFolio, RealPage, MRI, Entrata, or Buildium? Can they walk through a PM-specific phishing scenario and explain exactly what the response looks like? Do they have documented experience securing distributed PM operations across multiple properties?
A generalist MSP will give you a generic security stack. A PM-fluent partner will know that your leasing team’s Entrata logins are a higher-risk surface than your executive email accounts. That distinction matters when something goes wrong.
How Far Out Solutions Helps Property Management Companies Stay Secure
Cushman & Wakefield, Greystar, Lantower, and Watercrest Senior Living do not spend time worrying about whether their cloud PMS environments are secure. That is not because security is not a concern. It is because Far Out Solutions handles it.
Security for multifamily and commercial PM operators is not a new vertical for us. It is the work we have been doing long enough to know where the real gaps are and how attackers find them before you do.
Every account gets a vCIO, not a help desk ticket. Someone who knows your stack, your portfolio, and your operational calendar.
- Five-minute critical response time
- 99% client retention
- Enterprise-grade security stack.
- Unified property technology solutions
- Hands-on experience with Yardi, AppFolio, RealPage, MRI, Entrata, and Buildium
Cloud-Forward Does Not Mean Unprotected
Here is what this guide covered.
Your vendor secures the infrastructure. You secure everything on top of it. That line, the shared responsibility model, is where most PM companies are exposed without knowing it.
The attacks are active and specific to your industry. Fake PMS login pages harvesting credentials, ACH fraud targeting your accounting team, former employee accounts left open, and compromised third-party integrations. Three named PM companies were breached in the past year. Real estate is on Qilin’s target list.
Closing the gap does not require a security overhaul. It requires MFA on every account, access controls matched to job function, endpoint coverage across your portfolio, quarterly access reviews, and a team that knows what PM-specific phishing looks like before it hits your inbox.
The hard part is not knowing what to do. It is having someone make sure it actually gets done.
Start With a 72-Point Assessment
Your security posture is probably better than you think in some areas and worse than you realize in others. The only way to know is to look.
Far Out Solutions offers a 72-point assessment at no obligation. It covers your current environment across every platform your team touches, identifies the specific gaps, and gives you a clear picture of exactly where you stand.
Connect with Far Out Solutions to get started.





